Funny, i actually didn’t type commands in the console. I didn’t test that!
I only tested connecting mission planner to the MavProxy. I can have a try at this next week, if you want!
Yes please, thank you so much
Hi,
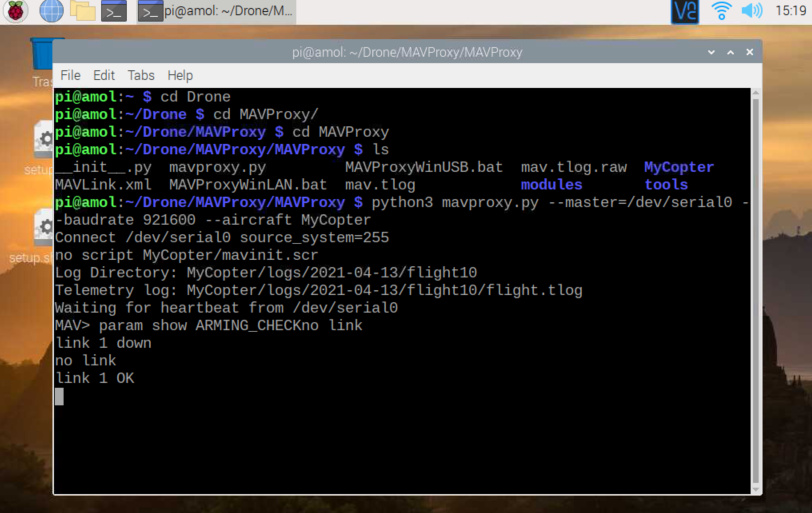
param show ARMING_CHECK does give a response to either, but then I connected mission planner and it suddenly showed:
Received 306 parameters
Saved 306 parameters to Drone450/logs/2017-09-07/flight3/mav.parm
After this, the command ‘param show ARMING_CHECK’ did work.
There is also a ‘param fetch’ command, but that doesn’t do anything. that seems like a bug.
i use via GPIO to connecting Raspi and Pixhawk.
And I use Telemetry to connect with Pixhawk and Mission Planner.
Raspi power is from USB
and Pixhawk power is from Battery
Could you teach me how to use “ls / dev” to know the port?
Teach me how to type it in Raspberry’s terminal, please 
in order to scan port services you can type
sudo screen “port_name” 57600
thankyou antpoli and everybody for your response 
hi,may i know how you solve this? i am facing the same problem now…
I created a pdf of what i did on my raspberry pi 4-b to install mavproxy please check out that
what_i_did.pdf (516.5 KB)
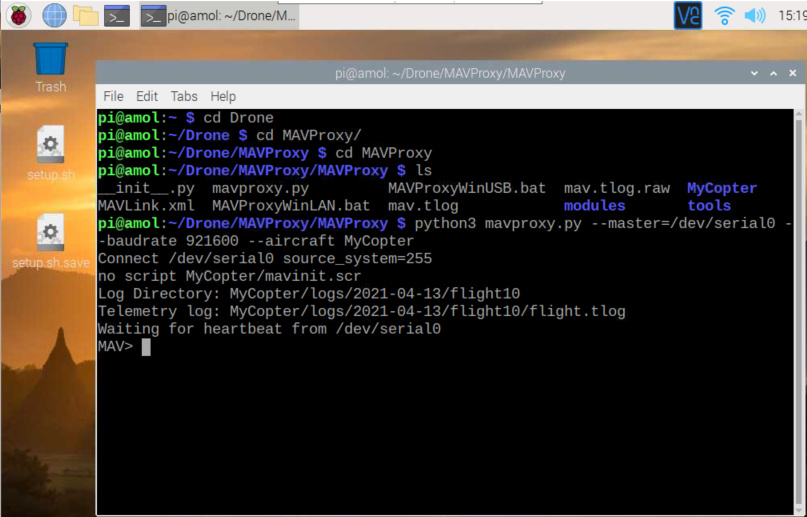
then by cloning from github
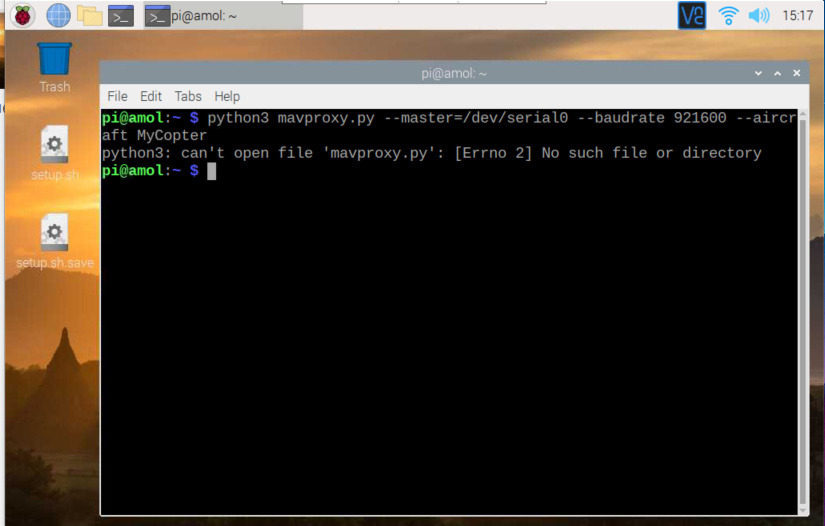
but whrn i run commands
nothing
Please guide me from starting step by step
I also had the problem that MavProxy blocked the entire Raspberry Pi after starting and it was not operable.
After being told to uninstall the ModemManager, I uninstalled the ModemManager and booted the Raspberry Pi. That was a very good approach, but MavProxy still shut down the Raspberry Pi. Nothing worked.
If you look at the generated serial port, it points to a device under /dev // in my case /dev/ttyACM0
ls -altr /dev/serial/by-id
lrwxrwxrwx 1 root root 13 Apr 26 16:21 usb-ArduPilot_speedybeef4v3_570047001350315141333220-if00 → …/…/ttyACM0
The rights of the device do not match. It cannot be accessed.
ls -al /dev/ttyACM0
crw-rw---- 1 root dialout 166, 0 Apr 26 16:34 /dev/ttyACM0
MavProxy only works after the rights for all have been set to read and write
sudo chmod a+rw /dev/ttyACM0
ls -al /dev/ttyACM0
crw-rw-rw- 1 root dialout 166, 0 Apr 26 16:42 /dev/ttyACM0
Now MavProxy works